AD FS and UAG are Better Together–Example of a real Solution
In the last nine posts we reviewed different topologies and discussed some of the techniques on how to integrate these topologies together. In this post we’ll take a look at real example of a production implementation.
The solution very similar to the following design has been implemented by one of the large enterprise companies. We will review it here in some detail. Every real world implementation is based on some type of specific requirements that the customer would like to satisfy. The solution is called “Application Gateway” or simply “Gateway”. The following are the main requirements that this solution must satisfy:
- Provide a secure infrastructure solution that can be accessed by users over the Internet.
- Provide an application portal to host applications for access by both internal and external users.
- Allow external users to create accounts.
- Allow external users to change their passwords.
- Provide external users with self-service password reset functionality.
- Allow internal users to leverage their current existing credentials for gaining access to the resources in this solution.
- Federated access to published applications by partner users.
- The solution must be secure, implemented in the DMZ environment, and ideally without Windows trusts between this solution environment and internal AD.
I just listed the main ones, but there are many more specific requirements. Those are not necessarily dictating the overall solution architecture.
The following software components are part of the solution, with Figure 1 showing how they relate to each other:
- FIM 2010 R2 – All IDM related functions
- Self-registration for external users
- SSPR for external users
- Group Management for application access AuthZ
- Approval Workflows for user creation
- UAG SP1 – External and Internal entry into the application hosting environment
- AD FS v2 – Authentication into the environment
- For external users access to SAML apps
- For internal users SSO to Gateway and access to SAML Apps
- SCOM/ACS – Monitoring and Audit
- AD – Directory Services
Figure 1: Solution Components
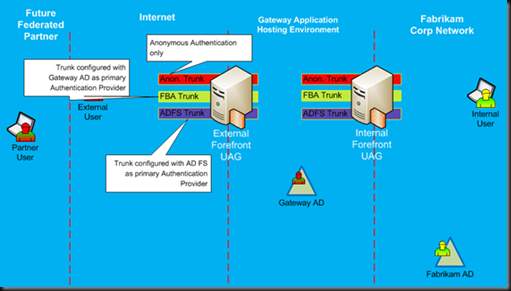
UAG Trunk Design in this solution will have at least three trunks on each UAG server, as shown in Figure 2.
- The first trunk will publish Anonymous applications. This trunk will be configured without any authentication requirements. The following are primary applications that will be published via this trunk:
- Initial landing page for users with menu selection of different tasks
- Self Service Password Reset application
- Self-User Registration application
- The second trunk will publish a portal for external users with password change function
- This trunk will use AD for primary authentication to the portal
- Will use AD FS as secondary for claims-enabled apps
- The third trunk will publish a portal for users authenticating via SAML (Federated)
- This trunk will use AD FS as the primary authentication to the portal
- It will be configured as a relaying party with RP-STS
Figure 2: UAG Trunks
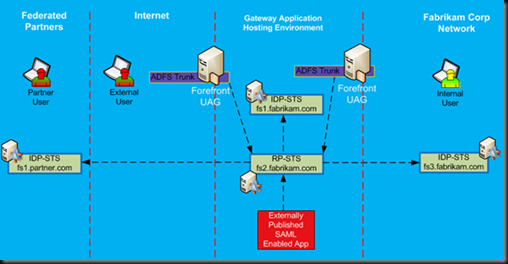
Figure 3 shows Federation configuration for this solution. It will have at least three AD FS Farms:
- The first farm will act as resource provider, and it will be configured with all applications in the Gateway application environment. All claims-enabled applications will trust this STS. In Figure 23, it is shown as RP-STS (fs2.fabrikam.com). As you can see, both UAG servers, specifically ADFS configured trunks, are some of the applications that are configured as relying parties with this RP-STS.
- The second AD FS server farm will provide SAML tokens to external users with accounts in the Gateway Active Directory. It will act as an identity provider to external users who have accounts in the Gateway AD. This STS is shown as IdP-STS (fs1.fabrikam.com). This STS will not be accessed via UAG as by means of UAG proxy. Instead it will be published on the FBA trunk as a secondary authentication provider.
- The third AD FS server farm will provide SAML tokens to internal users with accounts in Corporate Fabrikam AD. It will act as an identity provider to internal users. This STS is shown as IdP-STS (fs3.fabrikam.com). This STS is not published via UAG. In fact, it is providing Federated WebSSO to the RP-STS, so that internal Fabrikam users will be able to authenticate into the Gateway environment without being required to have a known UserID/Password in the Gateway AD.
Figure 3: Federation Design
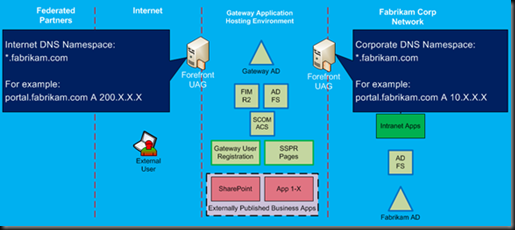
At this point, we need to review a very important technical requirement that must be satisfied for this solution to work. Internet facing UAG and internally exposed UAG must be resolved via the same DNS name. They must be identical. In other words, if an Internet based client types in the browser the name for this portal as portal.fabrikam.com, it should resolve to the external UAG IP address. At the same time, if internal user, using a computer on the corporate network is using the same URL, it should be resolved to the internal UAG server IP address. Why is this the case? It actually has nothing to do with UAG. This requirement comes from AD FS – the federation service URL always stays the same. In our example, if the client needs to get a SAML token from the fs2.fabrikam.com AD FS server, it must be able to resolve this URL and connect to it via that URL. Since this FS service is published via two different UAG servers, both sides of the users must be able access it via the same URL.
The easiest and most common way to satisfy this requirement is by having “split-brain” or dual zone DNS design. Basically, companies would have two different zones with the same name, one exposed to the Internet and one that is only internal. Figure 4 gives a visual demonstration of this requirement.
Figure 4: Split brain dual zone DNS design
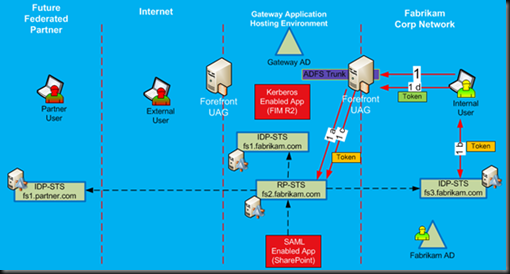
Let’s review how different users would authenticate into the Gateway and access published applications. First, we will start with internally based users. Figure 5 provides a high level flow of how internal users will authenticate to the internal UAG server. For internal users whose domain was federated with Gateway, they will use the ADFS trunk as their primary portal. When they try to authenticate, they will be using Federated WebSSO, with first step (1a) accessing RP-STS and performing a home realm discovery, which will redirect them to their internal IDP-STS in step 1b, where they get their initial SAML token, which will be provided back to RP-STS (step 1c). RP-STS will issue the final token, which the client will provide to the ADFS trunk (step 1d), and the user is authenticated to the portal.
Figure 5: Internal user authentication to UAG
After successful authentication, the user will see a list of applications published to him via the AD FS trunk. The authorization to see these applications must be done via contents of the claims. Using normal security groups from Gateway AD will no longer work because the internal user actually does not use Gateway AD for authentication to the portal.
There are two types of applications that are supported via AD FS enabled trunks: Kerberos Applications and Claims-enabled applications.
In this solution, FIM 2010 R2 must be published to the internal users so they can get into the FIM 2010 R2 portal and perform administrative tasks, such as approve or deny external user account requests. FIM R2 is not a claims-enabled application, but it is a Kerberos based application and it can be published via AD FS enabled trunk by using Kerberos Constrained Delegation. Of course for this to work, the Gateway AD must have a shadow account for internal users. FIM R2 will actually help with creating shadow accounts. It is configured to synchronize internal Fabrikam AD user accounts into the Gateway AD, thus creating a shadow account for internal users. It will not synchronize user passwords into Gateway AD.
Figure 6: Internal user accessing Kerberos Applications
Internal users will be able to access FIM R2 via SSO experience and perform their work as needed. Figure 6 shows the basic authentication step for Kerberos based application. In the future, this solution will be able to publish other Kerberos based applications, and they will be accessed in the same way as FIM 2010 R2. They will require proper SPN configuration and Gateway AD, but users will already have shadow accounts.
The other type of applications that can be published via AD FS enabled trunks are claims-based applications. These are easy and straight forward to publish and access via AD FS trunk. Figure 7 provides a high level authentication flow for internal users.
The interesting part in this authentication flow and what is different from the original authentication to the portal itself is the fact that the client does not need to get another security token from its internal IdP-STS. Since he is already authenticated to the portal, after the client tries to access the published application, the client browser will only need to request a new security token from RP-STS, specific for this application, as it shown in Figure 7.
Figure 7: Internal user accessing claims applications
Finally, we can examine authentication flow and application access by external users. There will be two types of external users: users with accounts registered in the Gateway AD for which they know their passwords and federated users, whose identity belongs to some other organization. Each user type will have to use different trunks for authentication.
External users with accounts in Gateway AD will be accessing it by using a UAG trunk with Gateway AD as the primary authentication provider. The primary reason for this configuration is to allow these users to change their passwords and to notify them when their password is about to expire. Trunks that use AD FS as the primary authentication provider do not provide password management functions.
Federated external users will access the portal via UAG trunks with the AD FS server as the primary authentication provider. While these users are important to the future of this solution, the current primary user base will consist of external users with accounts in Gateway AD, and, for this reason, Figure 29 shows the authentication flow and access to applications for these types of users only.
First, the user will need to authenticate into the portal, which will be done via UAG forms based authentication with Gateway AD account. After successful authentication into the portal, the user will be presented with a list of applications, which he/she has been authorized to access. The authorization is based on the AD group membership. The authentication flow to the application will depend on the application type.
Non-claims enabled applications are actually very straightforward. For example, FIM 2010 R2 will be published to external users by using SSO function of the UAG trunks, and it will use the same authentication provider as for the trunk itself. Users will access such applications by utilizing their AD credentials, with UAG taking care of this authentication behind the scenes and without any special type of configuration requirements. This flow is shown as step 2 to Kerberos enabled applications.
Authentication to claims-enabled applications will be a bit more complex. Figure 8 shows it with step 3 flow. The application is published via the FBA trunk portal, and the user will try to access it via that portal. With step 3a, it will contact the application and learn that the application trusts RP-STS. RP-STS is not published via FBA trunk. It is published via ADFS Trunk, a different trunk on the UAG server. In step 3b, the user’s browser will be redirected to the RP-STS to get the token for the target application. Theoretically, we could issue a SAML token at this point in time, but since RP-STS is not published via an FBA Trunk, we will not be able to provide SSO experience to the end user. If we would end the process here, the user would be required to authenticate to RP-STS. Since there is no SSO for this user on the ADFS trunk, he/she will be prompted for credentials. Instead, the Home Realm Discovery will happen, and the user will be redirected to the IdP-STS (fs1.fabrikam.com). IdP-STS is published on the FBA trunk, and it is configured with SSO authentication via Gateway AD. The user is already authenticated to the FBA trunk and via step 3c will authenticate to the IdP-STS and receive security token. This token will be posted back to the RP-STS in step 3d, which will be transformed into a new token, suitable for the target application. It will be provided back to the client computer and posted to the application via FBA trunk in step 3e. The application will authenticate the user and open in the user’s browser.
Figure 8: External User Authentication and Application Access
It is not the most straightforward authentication experience, but as discussed earlier in this paper, configuration of claims-based applications with multiple UAG trunks requires separation between Resource Provider STS and Identity provider STS. Otherwise it will not be published via different UAG trunks.
Authentication of a federated user via an external UAG server is done the same way. It is for internal Fabrikam users, straight forward federated WebSSO.
Things to know about this design:
During the implementation of this solution, we discovered a few restrictions in AD FS that would not be very obvious if we used only one UAG server. However with dual implementation and especially with identical name spaces on Internet and Intranet, we ran into some minor constraints. Fortunately, fairly easy workaround were quickly identified to bypass them.
The first constraint is related to the certificate usage on AD FS. It will not allow the use of the same certificate (certificate with the same hash) on multiple relying parties. Why is this a problem? Since we have the identical name space on the internal network and external network, originally we tried to save on costs and use the same wild card certificate (*.fabrikam.com) on external UAG and internal UAG servers. UAG servers will work just fine with the same cert, but when time came to set them up as relying parties on the AD FS RP-STS server, we encountered a problem. AD FS did not allow the creation of the second relying party with a certificate whose hash had already been used by another relying party. The simple solution to get around this problem is to issue two different wild card certificates, one for internal UAG and one for external UAG. Usually these certificates must be trusted by Internet clients, so you would need to get them from one of the commercial certificate providers, and it will double your cost.
The second constraint is related to the naming of the ADFS Trunks on external and internal UAG servers and the potential conflict with RP-STS Federation Services for each relying party. During ADFS trunk configuration on the UAG server, it is most logical to configure the public URL for the trunk to match the URL of the published Federation server. By default, you would probably create the ADFS trunk for fs2.fabrikam.com AD FS with the same URL, i.e. it will be fs2.fabrikam.com. Then you would proceed to configure AD FS with the UAG relying party, which will configure it with the Federation Service URL as fs2.fabrikam.com. So far so good, we have no issues. Now, we proceed with the configuration of the second UAG server, where we create the UAG trunk for internal users, with the same URL, to match RP-STS, ie, fs2.fabrikam.com. This is done without any issues on the UAG server. The second step in configuration will be the creation of the relying party trust on the AD FS server. AD FS will not allow you to create the relying party trust to the second UAG server. This is because it is using the same URL as the first one, and AD FS will not allow two relaying parties with the same URL. Fortunately, there is a workaround for this as well. All you need to do is to configure each ADFS trunk with its own unique URL, different from the RP-STS URL. For example, the external UAG AD FS Trunk can be configured with the following URL for its public name: fs2e.fabrikam.com, and internal UAG AD FS trunk can be configured with the following URL for its public name: fs2i.fabrikam.com. When configuring each UAG server with RP-STS, they will appear as different relying parties, and AD FS will be happy. One thing to remember is to make sure that DNS is configured to resolve fs2.fabrikam.com to each respective UAG trunk, i.e. it needs to point to the same IP address as its internal or external public trunks URLs.
Thanks!
From → AD FS, Cloud Security, Federation, Security, UAG




I have been reading over your blogs. I am in the process of trying to work out a solution with AD FS and UAG or really anything and I am running into a wall. All we are trying to do is pubish Sharepoint and have the users authenticate so that they are federated users. We have a webpart in Sharepoint for Office365 and in order to do SSO into their email, students need to be federated. All accounts are located on our AD server. I had it working with just AD FS with AD FS proxy except we cannot force students to change password at first login or do SSPR. So reading your blogs, would we have to do a three trunk solution? We have internal students and external students that may never touch a domain joined computer. We don’t want them to have to log in twice or even have the home realm discovery page if at all possible. Any thoughts or directions? We could even pay a contracted services if you would be williing.
LikeLike